Today’s enterprises are collecting, storing, and using more data than ever before. A 2022 IDG Research survey found that, on average, data volumes are growing by 63 percent per month across organizations.
No matter the size of the enterprise, the threat of data leaks and breaches of sensitive information are among the top priorities for senior executives. A single data breach can have serious and long-term consequences, especially if Personally Identifiable Information (PII) is involved.
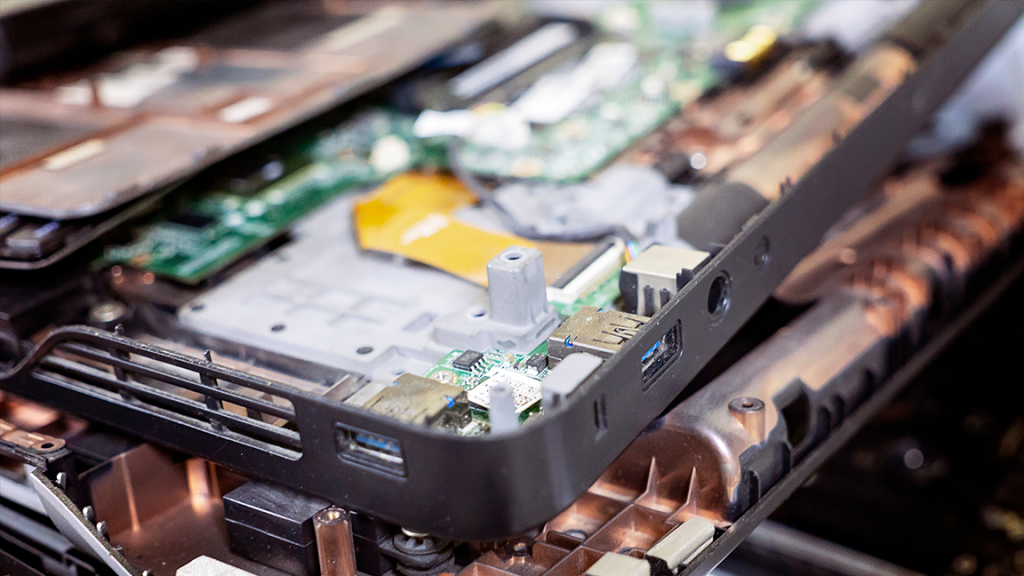
When decommissioning an on-premises or colocation data center, enterprises must take steps to ensure that data is effectively managed, migrated, sanitized, or destroyed. Sensitive data can be found on a wide range of hardware and devices, and IT teams must know where their data lives, how it is being used, and who is ultimately responsible for keeping it safe.
Fortunately, with proper planning and the help of an experienced IT services partner who knows and understands the data center environment, enterprises can mitigate the risk of a data breach and ensure IT assets, critical infrastructure, and other components are successfully decommissioned.
Know Where Your Data Lives
When thinking about sensitive data, most people immediately think of PII stored on hard drives.
But data is often found on far more inconspicuous devices, and this can open the organization up to increased risk.
Everything from routers to employee smart devices to printers can store data that, if not removed, can be accessed by third parties or malicious actors. Backup drives, flash drives, and other storage devices held outside of the cage are often overlooked by inexperienced IT Asset Disposition (ITAD) providers, simply because they are unfamiliar with these environments and unaware of what to look for when removing equipment.
In the same way, sensitive data is not solely limited to PII. Networking equipment, for example, typically stores network configurations and other critical setup data. In one example brought to the attention of our team, networking gear that retained this data was sold on the secondary market by another ITAD provider. Once installed in the new environment, it completely disrupted the network at the original company, and it took weeks for the problem to be fully resolved.
The difficulty for IT teams grows as organizations upgrade, refresh, and replace equipment. Lacking proper documentation and records, IT departments may have limited visibility into where their data is stored. As systems, applications, integrations, and hardware are cycled through the data center in response to business needs, it can be extremely difficult to untangle the mess of interdependencies and gain a clear picture.
However, this level of granularity is vital when decommissioning an enterprise data center. That’s why it’s so important that enterprises develop an accurate view of where data is stored, how sensitive it is, and what will be done with it before initiating the decommissioning project and removing equipment.
The Risk of Releasing Sensitive Data
Nearly all organizations understand the threat of a data breach and the risks involved with releasing sensitive data. In fact, a recent survey found that a full 96 percent of enterprises have a data sanitization policy in place.
However, simply having a policy is not enough. Of those with a policy, only 44 percent believed they have fully implemented it and that the policy has been effectively communicated across the entire business.
Given this lack of clarity, it should be no surprise that devices are regularly resold with sensitive data on them. Another survey showed that 40 percent of devices resold in regular commerce channels contained PII that was relatively easy to access.
As mentioned, the consequences of a data breach can be severe and long-lasting. In one recent case, Morgan Stanley agreed to pay $60 million to settle a claim that it failed to safeguard PII when decommissioning data center equipment. In addition to fines and penalties, a data breach can result in reputational damage, lost business, and ongoing costs to recover or safeguard the data.
Data Sanitization and Destruction
Before decommissioning the data center, enterprises should develop an accurate and complete list of all devices that store sensitive data. They should also determine what approach they will take to remove the data when disposing of used assets.
Assets that still work and have residual value on secondary markets can be resold. By recovering this asset value, enterprises can offset the cost of the decommissioning project and keep e-waste out of landfills.
In these cases, data sanitization techniques permanently and irreversibly remove the data to make it unrecoverable. There are a few different sanitization methods, but they all allow the device to be reused without the risk that data is recovered or accessed.
In cases where the hardware does not have any residual value, it can be physically destroyed by shredding or other destruction techniques. This makes the data inaccessible but also renders the device unusable.
Mitigating Risk When Decommissioning the Data Center
Data breaches are a significant risk for enterprises, and any release of sensitive information can result in serious consequences. This risk is heightened when decommissioning the data center, as enterprises are often focused on removing the equipment in time, avoiding downtime and outages, and migrating applications and workloads to the new site.
By developing an accurate and granular picture of where data is stored, determining and communicating policies for effective sanitization or destruction, and working with an experienced IT services partner who understands the data center environment, enterprises can mitigate the risk of a breach and keep their data safe and secured throughout the decommissioning project.